Preassessment
1. Sarah works as an auditor in an organization. She completed an audit of a project, carried out the examination, and collected all the evidence. All these are included in the evidence report. An initial meeting was held in which the evidence report was reviewed by the audited party prior to release to head off any misinformation or misinterpretation. After the initial meeting, she prepared a report in the closing meeting with all parties. Which of the following are included in the report generated by Sarah?
Each correct answer represents a complete solution. Choose all that apply.
Preliminary conclusions
Problems experienced
Recommendations for remediation
2. Why is examining designs and implementations for single points of failure in a product or a system important?
To prevent a form of catastrophic failure from being released in the product or system
3. Which of the following phases of the SDL process must prepare the organization for potential issues coming in from the field, and includes the preparation of the incident response plan to be used in the response phase?
Release
4. Which of the following statements are true about penetration testing?
Each correct answer represents a complete solution. Choose all that apply.
It harnesses the power of the human intellect to make a more targeted examination.
It is designed to mimic the attacker’s ethos and methodology.
It is an active form of examining the system for weaknesses and vulnerabilities.
It involves testing the application in an environment that mirrors the associated production environment.
5. Suppose a system is connecting to a database to verify user credentials. An error occurred, as in the database, the credentials are not available when the request is made, and the system needs to properly deal with the case. The system should not inadvertently grant access in the event of an error. The system may need to log the error, along with information concerning what caused the error, but this information needs to be protected. Releasing the connection string to the database or passing the database credentials with the request would be a security failure. Which of the following processes is explained in the given example?
Exception management
6. Which of the following options refers to defining security relations with respect to the container?
Declarative security
7. Which of the following is a framework and methodology for developing risk-driven enterprise information security architectures and for delivering security infrastructure solutions that support critical business initiatives?
SABSA
8. Charlotte is having a dispute with a co-worker, Hank, over access to the information contained in a database maintained by his department. She needs the information to carry out her job responsibilities, while he insists that nobody outside the department is allowed to access the information. She does not agree that the other department should make this decision, and her supervisor agrees with her. Which type of policy could she turn to for the most applicable guidance?
Data ownership
9. Which of the following is a graphical representation of an attack, beginning with the attack objective as the root node?
Attack tree
10. Which of the following is explained in the statement given below?
“It records and prepares reports that show the status and history of controlled software items, including baselines.”
Configuration status accounting
11. Martha is the project manager of a shipbuilding project. She, with her team, is creating a table that links needs to their origin and traces them throughout the project lifecycle. Which of the following defines the table that she is creating in the given scenario?
RTM
12. The operations process is dependent on configuration management to enforce the necessary control during the problem resolution process itself. Which of the following are the consequences of this dependency?
Each correct answer represents a complete solution. Choose all that apply.
There is an explicit requirement that any change requests submitted to operations must be monitored to their conclusion.
There is a sign-off from configuration management obtained once completion conditions have been satisfied.
13. You are a project manager in a company. You are responsible for website security in your company and want to address widely known and documented web application vulnerabilities. Which of the following is a resource that would be most helpful in the given scenario?
OWASP
14. Which of the following statements are true about concurrency?
Each correct answer represents a complete solution. Choose all that apply.
It is an issue when the threads access a common object, creating a shared object property.
It is the process of two or more threads in a program executing concurrently.
15. Which of the following performs specific database activities automatically that are executed in response to specific database events?
Trigger
16. If the software is secure but is lacking in quality, then undocumented features may exist. Which of the following options can be the result of undocumented features?
Improper or undesired behaviors
17. Which of the following statements are true about supplier risk assessment?
Each correct answer represents a complete solution. Choose all that apply.
It is an information-gathering function that focuses on understanding the consequences of all feasible risks.
It is used to identify specific threats to the organization’s supply chain.
It identifies what could go wrong in the development process.
It allows customers to deploy the necessary proactive and reactive controls to respond to threats as they arise in the supply chain.
18. Juan works in an investigating department. He gathers the evidence that can be used in court to convict persons of crimes. Which of the following is used to address the reliability and credibility of the evidence?
Chain of custody
19. Taylor, a penetration tester, requires multiple layers of security controls to be placed throughout an IT infrastructure, which improves the security posture of an organization to defend against malicious attacks or potential vulnerabilities. Which of the following will she use?
Defense in depth
20. Which of the following is a series of technologies employed so that content owners can exert control over digital content on their systems?
DRM
21. Jack uses a programming language to encode the specific set of operations in what is referred to as source code. Which of the following is the designation of Jack?
Software developer
22. An attack is performed on a web application where a string of characters is entered and input validation is bypassed to display some additional information. Which attack is being performed in the given scenario?
SQL injection
23. Your company is about to invest heavily in an application written by a new startup. Because it is such a sizable investment, you express your concerns about the longevity of the new company and the risk this organization is taking. You propose that the new company agree to store its source code for use by customers if it ceases business. Which of the following is explained in the given scenario?
Code escrow
24. You are being tasked by your organization to create a statement of work that will be utilized in the software lifecycle. The legal department explains to you that they want to make sure that all terms and conditions are negotiated and agreed to up front. Then, when the scope needs to be changed, there is more flexibility in the process. Which of the following is a type of agreement that the legal department is referring to?
SLA
25. Which of the following are the uses of the CWE/SANS Top 25 list?
Each correct answer represents a complete solution. Choose all that apply.
It is used as a tool for development teams to provide education and awareness about the kinds of vulnerabilities that plague the software industry.
It is used in software procurement as a specification of elements that need to be mitigated in the purchased software.
26. An organization wants to identify the top threats that have the greatest potential impact to the organization. Which of the following steps should be taken first to detect all of the possible threats in a single pass?
Identifying security objectives
27. The design and execution of qualification tests themselves are normally dictated in the contract. That usually includes consideration of which of the following things?
Each correct answer represents a complete solution. Choose all that apply.
Requisite load limits
Requisite performance levels
Test cases to address questions
Number and types of load tests
28. Which of the following statements are true about management V&V review?
Each correct answer represents a complete solution. Choose all that apply.
It examines administrative plans, schedules, requirements, and methods for the purpose of assessing their suitability for the project.
It is carried out for the purpose of supporting the administrative personnel who have direct responsibility for a system.
29. A testing method is performed in which individual components of the software are tested. What type of testing does this describe?
Unit
30. Hazel works as a software developer in an organization. She started the process to create a set of security testing controls for her project. Firstly she initiates the process. Then she identified the relevant security testing issues for each level and components in the supply chain process. Which of the following will be her next step in the given scenario?
Creating a generic security testing plan
31 Which of the following statements are true about OSSTMM?
Each correct answer represents a complete solution. Choose all that apply.
It is a peer-reviewed system describing security testing.
It provides a scientific methodology for assessing operational security built upon analytical metrics.
It is used to assist in auditing.
It addresses security engineering activities that span the entire trusted product or secure system lifecycle.
32. Which of the following can provide management information as to the effectiveness of and trends associated with security processes?
Metric
33. Roma works as a security worker for a company. She has been asked to design a development model using the various security tenets and design principles incorporating confidentiality, integrity, least privilege, separation of duties, and so on. Which of the following will she use to design the development model in the given scenario?
SDL
34. Your organization has asked you to develop a security model by keeping in mind that the confidentiality of data should be of utmost priority. Which of the following security models will you develop?
Bell-LaPadula
35. If a user faces cross-site scripting and injection vulnerability issues, which of the following testing should the user choose?
Fuzz testing
36. Which of the following controls is designed to act when a primary set of controls has failed?
Compensating
37. You have been hired as a security consultant for an organization that does contract work for the U.S. Department of Defense (DoD). You must ensure that all data that is part of the contract work is categorized appropriately. What is the highest degree of data protection category you can use in the given scenario?
Top Secret
38. You have identified the risks and now you need to mitigate those risks as you find them unacceptable. Once you treat the risks, you won’t completely eliminate all the risks because it is simply not possible and therefore, some risks will remain at a certain level. This is a description of which of the following?
Residual risk
39. Which of the following are general external security requirements required to craft solutions?
Each correct answer represents a complete solution. Choose all that apply.
Employ content filtering and proxies to protect against web-based threats.
Manage outer connections with security controls.
Manage outer connections and authentication.
Manage data loss prevention elements.
40. What is the goal of tracking bugs?
To ensure that at some point, the flaws or glitches in a system get addressed by the development team
41. Mary works as an IT security analyst for an organization that researches and archives old music. Her collective exchanges music files in two forms: images of written sheet music and electronic copies of recordings. What intellectual property legal construct is protected by both of these?
Copyright
42. Which of the following are specific legal issues that have significant risks to an enterprise?
Each correct answer represents a complete solution. Choose all that apply.
Data breach event
Intellectual property
43. Which of the following data should be concealed to protect it from unauthorized disclosure using obfuscation techniques?
Hidden
44. Which of the following makes it easy for the developer to do both forms of static and dynamic checking automatically?
IDE
45. Tom works as a project manager in an organization. He is using a development model for his project. Now, in between the projects, he wants to add a resource in the process, but he is not able to add it. Which of the following models is he using that has the limitation mentioned in the given scenario?
Waterfall
46. In James’ company, users change job positions on a regular basis. James would like the company’s access control system to make it easy for administrators to adjust permissions when these changes occur. Which model of access control is best suited for James’ needs?
Role-based
47. Which of the following is a list of standard identifiers for known software vulnerabilities that have been found in software?
CVE
48. In __________ testing, the attacker has no knowledge of the inner workings of the software under test.
black-box
49. Alicia works as a software developer in an organization. She is facing an issue while developing software. So, she decided to use patches. The issue is fixed, but the fix started causing some other issues. Which of the following can be the issues that started occurring in the given scenario?
Each correct answer represents a complete solution. Choose all that apply.
The fix may repair a special case, entering a letter instead of a number, but miss the general case of entering any non-numeric value.
The fix may cause a fault in some other part of the software.
The fix may undo some other mitigation at the point of the fix.
The fix may cause the creation of duplicate software.
50. Which of the following CMMI levels focuses on process improvement?
Optimizing
51. Due to new regulations, an organization has decided to initiate an organizational vulnerability management program and assign the function to the security team. Which of the following frameworks would support the program?
Each correct answer represents a complete solution. Choose two.
ITIL
OWASP
52. An organization has recently suffered a series of security breaches that have damaged its reputation. Several successful attacks have resulted in compromised customer database files accessible via one of the company’s web servers. Additionally, an employee had access to secret data from previous job assignments. This employee made copies of the data and sold it to competitors. The organization has hired a security consultant to help reduce the risk of future attacks. What would the consultant use to identify potential attackers in the given scenario?
Threat modeling
53. An organization has recently suffered a series of security breaches that have damaged its reputation. Several successful attacks have resulted in compromised customer database files accessible via one of the company’s web servers. Additionally, an employee had access to secret data from previous job assignments. This employee made copies of the data and sold it to competitors. The organization has hired a security consultant to help reduce the risk of future attacks. What would the consultant use to identify potential attackers in the given scenario?
Threat modeling
54. John is a penetration tester. He is performing a test that relies on the execution of the code while performing it with input to test the software. This type of testing has a strong preference for automated testing tools due to the volume of tests that need to be conducted in most specialized automation code testing processes. Which type of testing is he performing?
Dynamic
55. Chris works as project manager of the ABC project in an organization. He wants to execute a process to determine the impact of events that are affecting his project objectively. The process he chose involves the use of metrics and models. Which of the following processes did Chris choose to accomplish his task in the given scenario?
Quantitative risk assessment
56. Alex works as a software developer in an organization. He wants to examine configuration issues and how they affect the program outcome and data issues that can result in programmatic instability can also be investigated in the simulated environment. Which of the following tests can he choose to accomplish his task?
Simulation testing
57. James is working as a product manager at NilCo. The Management has asked him to deploy some new infrastructure with the updates and changes without implementing them directly on the production server. The deployment should occur in a procedural and repeatable fashion. Which of the following will he use to accomplish this task?
Bootstrapping
58. Adam is conducting software testing by reviewing the source code of an application. Which code analysis method is he performing?
Static
59. Jack is staging an attack against Laura’s website by embedding a link on her site that will execute malicious code on a visitor’s machine if the visitor clicks on the link. This is an example of which type of attack?
Cross-site scripting
60. Which of the following access control mechanisms are employed by the Bell-LaPadula security model when implementing its two basic security principles?
Each correct answer represents a complete solution. Choose all that apply.
Mandatory
Discretionary
61. You have completed the development of several features of a new software application. You plan to provide an early look at the product to important customers to gather some feedback. Your application still misses features, and you haven’t yet optimized the application for performance and security. Which kind of testing should you perform with a limited number of customers?
Alpha
62. Jack works as a network administrator in an organization. To protect his organization from malicious intruders, misbehaving programs, and similar attacks, he would like to implement a specialized firewall. Which technology should he choose for the implementation process explained in the given scenario?
Application firewall
63. You work as a release manager for uCertify.com. You are overseeing and managing the release management process in your organization. What are the benefits of performing this process?
Each correct answer represents a complete solution. Choose all that apply
It addresses the need to maintain confidence in the integrity of the product.
It is designed to ensure the integrity of the baselines of a given product.
It ensures the inherent correctness of software products or updates.
It controls the release and delivery of modifications through the library function.
64. Which of the following best describes the SMART acronym that helps organizations to make goal setting more explicit?
Specific, Measurable, Assignable, Realistic, and Time bound
65. Which of the following steps of the SEI model converts the risk data gathered into information that can be used to make decisions?
Analyze
66. Which of the following is the process by which application programs manipulate strings to a base form, creating a foundational representation of the input?
Canonicalization
67. Ryan works as a software developer in an organization. He worked on a program and used programmatic response for the occurrence of anomalous conditions that occur during the operation of a program. Which of the following is a response he is referring to in the given scenario?
Exception management
68. Which of the following evaluates the software product itself, including the requirements and design documentation?
Technical V&V
69. Samson works as a security analyst in an organization. He wants to create a system that can accurately characterize the security of an operational system in a consistent and reliable fashion. So, to create such a system, he needs a process. Which of the following can he use to accomplish his task in the given scenario?
OSSTMM
70. Which of the following statements are true about OpenID?
Each correct answer represents a complete solution. Choose all that apply.
It was created for federated authentication, specifically to allow a third party to authenticate your users for you by using accounts that users already have.
Its protocol enables websites or applications to grant access to their own applications by using another service or application for authentication.
71. Which of the following statements are true about scanning?
Each correct answer represents a complete solution. Choose all that apply.
It is an automated enumeration of specific characteristics of an application or network.
It is used in software development to characterize an application on a target platform.
It provides the development team with a wealth of information as to how a system will behave when deployed into production.
It is used to measure the security impact of an application on a Windows environment.
72. Which of the following is defined in the statement given below?
“It is defined as a complete set of backups needed to restore data. This can be a full backup set or a full backup plus incremental sets.”
Retention cycle
73. Peter works as a software developer in an organization. He installed an application on the Windows OS and now he wants to detect the changes that occur to the underlying Windows OS. Which of the following options can he use to accomplish his task?
Attack surface analyzer
74. Which of the following is a means of documenting the software, tools, samples of data input and output, and configurations used to complete a set of tests?
Test harness
75. Which of the following statements are true about use case?
Each correct answer represents a complete solution. Choose all that apply.
It determines functional requirements in developer-friendly terms.
It is constructed of actors representing users and intended system behaviors.
76. The management at Revaan’s company has asked him to implement an access control system that can support rule declarations like “Only allow access to salespeople from managed devices on the wireless network between 8 a.m. and 6 p.m.” What type of access control system would be Revaan’s choice?
Attribute-based access control
77. Which of the following is a common practice that is used to maintain the security of sensitive data?
Tokenization
78. Mary works as a security analyst in an organization. She notices a vulnerability in one of the systems. She found out that some hackers are intentionally trying to exploit a network vulnerability to run arbitrary code on a targeted machine or system. Which of the following describes the vulnerability faced by Mary in the given scenario?
RCE
79. Refer to the following figure:
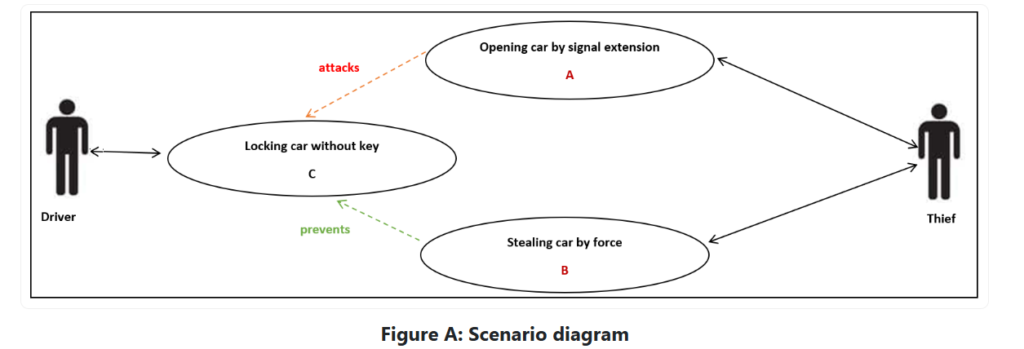
80. Which of the following is an approach that explains A and B tasks in the scenario given in the figure?
Misuse case
81. Which of the following is the extent to which a programming language prevents errors resulting from different data types in a program?
Type safety
82. You are a project manager for Star Light Strings. Star Light manufactures strings of lights for outdoor display. Its products range from simple light strings to elaborate lights with animal designs, bug designs, memorabilia, and so on. Your newest project requires a change. You have documented the characteristics of the product and its functionality. Which of the following have you used for documenting the characteristics in the given scenario?
Configuration management
83. Which of the following is frequently found during activities such as penetration testing and fuzz testing?
Vulnerabilities
84. An organization has created an access control policy that grants specific privileges to accountants. What type of access control is this?
Role-based access control
85. Which of the following statements are true about the version control system?
Each correct answer represents a complete solution. Choose all that apply.
It handles all the questions asked by the management team.
It tracks all the pieces of a project and enables complete management.
It manages access to source files, locking sections of code so that only one developer at a time can check out and modify pieces of code.
It stores information on a user’s computer by a web server to maintain the state of the connection to the web server.
86. Which of the following sources of business risk is the deliberate deception made for personal gain to obtain property or services?
Fraud
Max, an attacker, has found a hidden button on the web page of an XYZ website. Using features of the browser, he unhides the button and then clicks it to perform a task that only the system administrator should be able to perform. Which of the following security elements is he violating in the given scenario?
Authorization
Which of the following statements is not true about peer-to-peer architecture?
It implies a separation of duties and power.
Jim is performing the configuration management process. He performed process implementation and the configuration identification process. Which of the following will be his next step in the given scenario?
Configuration control
You might write code that prevents users from entering certain data values that might present a security problem. Which of the following is associated with the given scenario?
Mitigation
Which of the following are the classes of web services that are identified by W3C under the Web Services Architecture?
Each correct answer represents a complete solution. Choose all that apply.
Arbitrary
REST-compliant
Which of the following can determine if single or multiple bits of data change from the original form?
Hash function
An organization is having an asset value of $800,000 and an exposure factor of 50%. What will be the single loss expectancy (SLE) for the organization?
$4,00,000
Sam, a penetration tester, is asked to perform a penetration test from an external IP address with no prior knowledge of the internal IT systems. What kind of test will Sam perform?
Black-box
Jack works as a software developer in an organization. When designing configuration setups, he recognized the level of protection needed. So, he wants protection at the simplest level for his data in a directory. Which of the following can he use for the required security in the given scenario?
ACL
Which of the following are ideal times for checking for and ensuring mitigation against certain types of errors?
Code walkthroughs
You receive an email from the customer support of an online shopping website, which you frequently visit, telling you that they need to confirm your credit card information to protect your account. The email urges you to respond quickly to ensure that your credit card information isn’t stolen by criminals. Without thinking twice and because you trust the online store, you send not only your credit card information but also your mailing address and phone number. A few days later, you receive a call from your credit card company telling you that your credit card has been stolen and used for thousands of dollars of fraudulent purchases. Which of the following attacks is explained in the given scenario?
Social engineering
Within an X.509 digital certificate, which of the following identifies the CA that generated and digitally signed the certificate?
Issuer
Which of the following statements are true about Syslog?
Each correct answer represents a complete solution. Choose all that apply.
It is an IETF approved protocol for log messaging.
It is designed and built around UNIX and provides a UNIX-centric format for sending log information across an IP network.
An attack on your web application began with a long string of numbers sent to a field that’s only supposed to hold a four-digit variable. What are the root causes of the vulnerability?
Each correct answer represents a complete solution. Choose all that apply.
Programming language weaknesses
Poor programming practice
Which of the following are primary mitigations?
Each correct answer represents a complete solution. Choose all that apply.
Integrate security into the entire software development lifecycle.
Establish and maintain control over all of your outputs.
Use libraries and frameworks that make it easier to avoid introducing weaknesses.
Assume that external components can be subverted and code is unreadable.
Which of the following is an attack that is against the implementation of a cryptosystem, rather than the strength of the algorithm itself?
Side channel

Comments
Post a Comment